This section explains how to integrate Deepnet DualShield Authentication Platform 5.6 or higher with Parallels RAS.
You may also read the following documentation on DualShield Authentication Platform:
DualShield Authentication Platform – Installation Guide
DualShield Authentication Platform – Quick Start Guide
DualShield Authentication Platform – Administration Guide
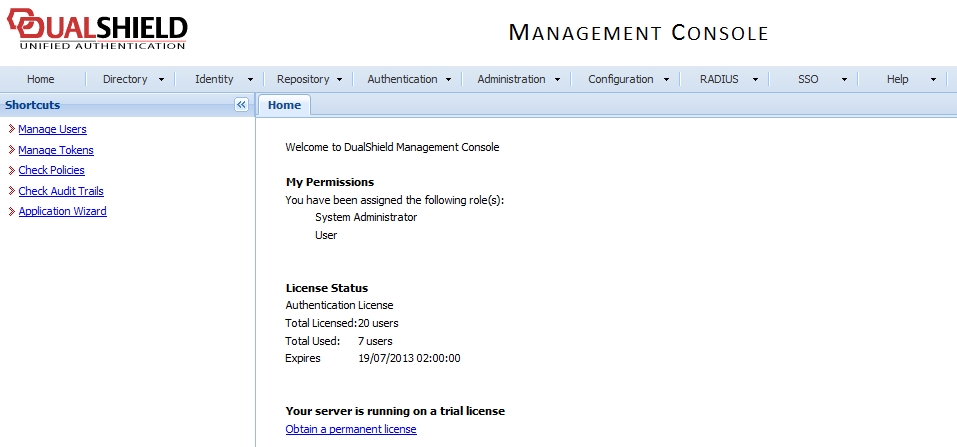
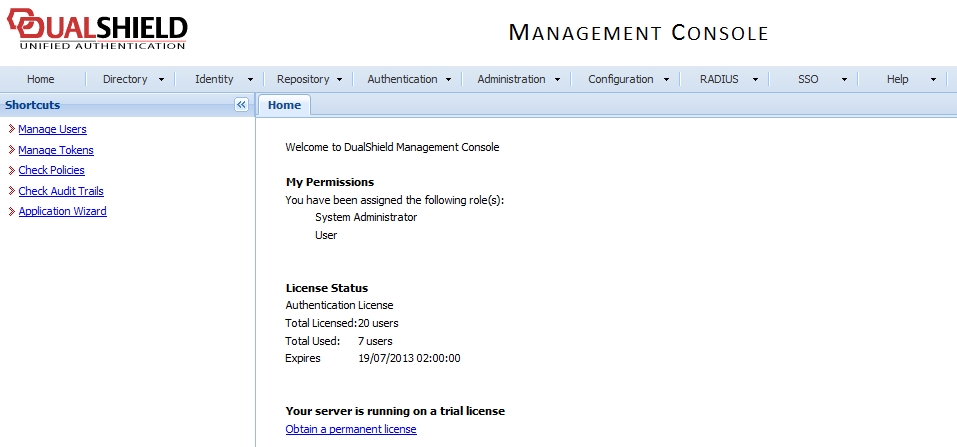
After following all the specified steps in "DualShield Authentication Platform – installation Guide" a URP is automatically opened in your internet browser (http:// LOCALHOST:8073) which allows you to logon to the Management Console of DualShield.
Login in to the DualShield Management Console with the default credentials (User: sa, Password: sa). You will be prompted to change the default password.
Applications are set to provide a connection to realm, as the realm contains domains of users who will be allowed the access to the application.
Realm is set for multiple domain users to be able to access the same application.
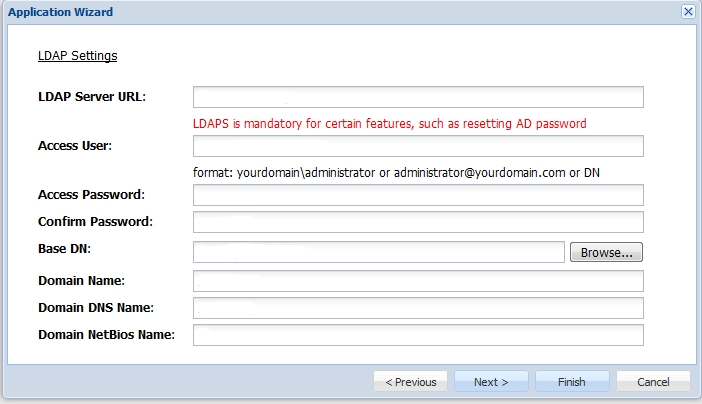
You need to create an Application which Parallels RAS will communicate with. Click on Authentication > Application Wizard and enter the information shown below and press Next.
Specify the LDAP Server settings as shown below and press Finish.
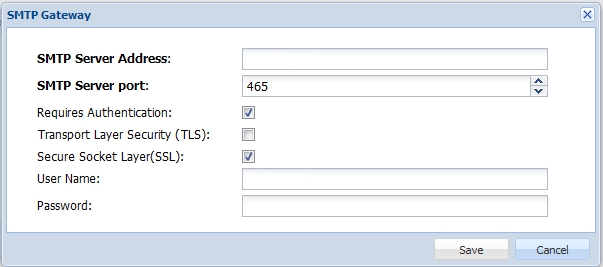
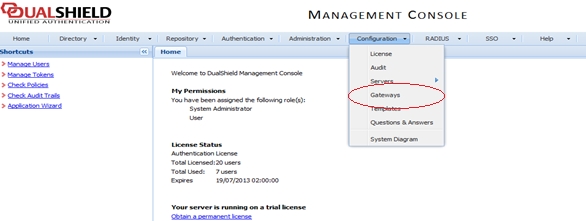
After you have configured the application you need to configure an Email or SMS gateway which are used by DualShield server to communicate with the end user. In this document we will be using an Email gateway. Select Gateways from the Configuration menu.
Configure your email gateway.
Click Edit to enter your SMTP server information
The following is the list tokens supported by Parallels RAS:
MobileID (FlashID is not integrated with MobileID)
QuickID
GridID
SafeID
SecureID (RSA)
DigiPass (Vasco)
If using hardware tokens such as SafeID the token information must first the XML file provided. Click on ‘Import’ and browse for the XML file provided. After the XML file has been imported each hardware token must be assigned to a user.
Once DualShield has been enabled the users will have two-factor authentication. If using software tokens such as QuickID the administrator does not have to create a token for each user. RAS Connection Broker will automatically create the token when the user tries to log in for the first time.
When a user tries to access a RAS Connection from Parallels Client, they are first prompted for the Windows username and password. If the credentials are accepted, RAS Connection Broker will communicate with the DualShield server to create a unique token for that user.
If using MobileID or QuickID, an email about where to download the appropriate software will be sent to the user.
If using QuickID tokens, the application will ask for a One-Time Password which is sent by e-mail or SMS.
When asked for OTP, enter the One-Time Password to log in to the Parallels ApplicationServer XG Gateway.
To configure Deepnet DualShield settings:
Specify the following:
Server: Hostname of the Deepnet server.
Enable SSL: Whether to use SSL when connecting to the Deepnet server.
Port: Port used for connection to the Deepnet server.
Agent: Agent name that will be used during registration.
Click the Check Connection button to test that the authentication server can be reached and to verify that the RAS Console is registered as a DualShield agent. If you see the "DeepNet server not valid" message, it could be dues to the following:
The specified server information is incorrect
You need ot allow auto registration of the Parallels components as a DualShield agent.
If you need to allow auto registration of the Parallels components as a DualShield agent, do the following:
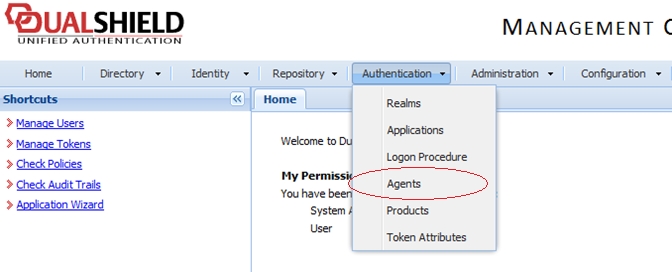
Go back to the DualShield Management Console and select Agents from the Authentication menu as shown below.
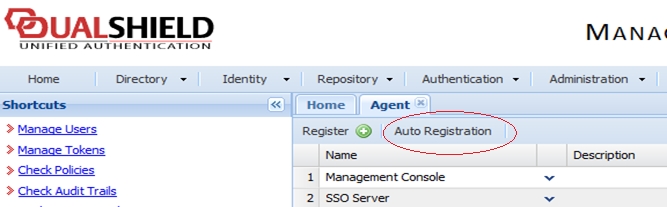
Select Auto Registration.
Select the Enabled option and set the date range.
Once the Agent Auto Registration is set, go back to the RAS Console and select Yes. You should see a message that the Dual Shield agent has been successfully registered.
Please note that all RAS Connection Brokers must be registered with Deepnet DualShield server. If you are using secondary Connection Brokers, you need to close all open windows until you can press Apply in the RAS Console. This will inform all the agents to self-register as DualShield agents.
Go back to the RAS Console and click Next.
Specify the following:
Application: Name of the Application created in Configuring DualShield 5.6+ Authentication Platform.
Default domain: Domain that will be used if the domain was not specified by the user, in the Theme properties or in the Connection settings.
In the Mode drop-down list, and select how you want your users to be authenticated:
Mandatory for all users means that every user using the system must log in using two-factor authentication.
Create token for Domain Authenticated Users will allow Parallels RAS to automatically create software tokens for Domain Authenticated Users. Choose a token type from the drop-down list. Note that this option only works with software tokens, such as QuickID and MobileID
Use only for users with a DualShield account will allow users that do not have a DualShield account to use the system without have to login using two-factor authentication.
In the Allow channels section, select the channels that will be used to send OTPs to users.
Click Finish.